Unveiling the Power of Open Source Intelligence (OSINT) in Combating Cyber Crime

In the ever-evolving digital landscape, cyber crime has become a formidable threat, posing significant risks to individuals, businesses, and governments alike. Combating these sophisticated attacks requires a comprehensive approach, including the utilization of Open Source Intelligence (OSINT) techniques. This article aims to shed light on the critical role of OSINT in the fight against cyber crime, empowering investigators, analysts, and security professionals with the knowledge and tools they need to effectively address this growing menace.
4 out of 5
| Language | : | English |
| File size | : | 30021 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 434 pages |
Defining Open Source Intelligence (OSINT)
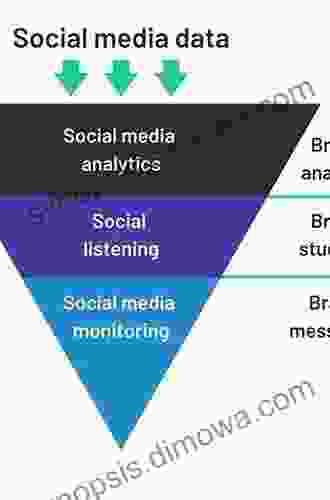
Open Source Intelligence refers to the collection and analysis of publicly available information from diverse online and offline sources. Unlike classified or proprietary data obtained through covert operations, OSINT leverages publicly accessible sources such as social media platforms, websites, news articles, public records, and online repositories. This vast pool of data provides valuable insights into individuals, organizations, and events, enabling researchers to uncover hidden connections, identify potential threats, and support criminal investigations.
The Role of OSINT in Combating Cyber Crime
OSINT plays a pivotal role in various aspects of cyber crime investigations, including threat intelligence gathering, incident response, and forensic analysis. Let's delve into each of these areas:
Threat Intelligence Gathering
OSINT empowers investigators and analysts to proactively identify potential cyber threats by monitoring social media, online forums, and dark web marketplaces. By analyzing public discussions, identifying suspicious activity, and tracking threat actors, security professionals can gain valuable insights into emerging threats, enabling them to develop timely countermeasures.
Incident Response
In the event of a cyber incident, OSINT can provide critical information to guide the response efforts. By swiftly gathering data from public sources, investigators can quickly identify the source of the attack, determine its scope and impact, and trace the movements of threat actors. This real-time intelligence empowers responders to contain the incident, mitigate damages, and apprehend the perpetrators.
Forensic Analysis
OSINT techniques are also instrumental in digital forensics, where investigators analyze digital evidence to uncover hidden connections and identify potential suspects. By examining public profiles, social media connections, and online activity, forensic analysts can link digital artifacts to individuals and organizations, revealing their involvement in cyber crimes.
Benefits of OSINT for Cyber Crime Investigations
Leveraging OSINT in cyber crime investigations offers numerous benefits, including:
* Cost-effectiveness: Unlike traditional intelligence gathering methods, OSINT is largely free to access, making it a cost-effective solution for resource-constrained organizations. * Accessibility: Publicly available data is readily accessible to anyone with an internet connection, empowering a wider range of investigators and analysts to contribute to cyber crime investigations. * Timeliness: OSINT allows for rapid threat detection and incident response, as publicly available information can be gathered and analyzed in real-time. * Legal compliance: OSINT relies solely on publicly available data, ensuring compliance with data privacy regulations and ethical guidelines.
Challenges of OSINT in Cyber Crime Investigations
While OSINT offers significant benefits, it also presents certain challenges that must be addressed:
* Data overload: The vast amount of publicly available data can be overwhelming, making it difficult to sift through and identify relevant information. * False positives: Analyzing OSINT data can yield false positives, leading to inaccurate s and wasted resources. * Data manipulation: Threat actors can deliberately manipulate publicly available information to mislead investigators and conceal their activities. * Anonymity and encryption: Cyber criminals often employ anonymizing techniques and encryption to evade detection, making it challenging to trace their online activities.
Best Practices for OSINT in Cyber Crime Investigations
To effectively harness the power of OSINT in cyber crime investigations, it is essential to adhere to the following best practices:
* Use specialized tools: Utilize specialized OSINT tools and platforms to efficiently collect and analyze large volumes of data. * Verify and cross-reference information: Corroborate findings from multiple sources to minimize the risk of false positives. * Collaborate with experts: Engage with domain experts, such as forensic analysts and threat intelligence specialists, to gain specialized insights. * Stay up-to-date: Continuously monitor emerging trends and techniques in the field of OSINT to ensure your knowledge and skills remain current.
Open Source Intelligence (OSINT) has emerged as an indispensable tool in the fight against cyber crime. By leveraging publicly available data, investigators and analysts can uncover hidden connections, identify potential threats, and support criminal investigations. The cost-effectiveness, accessibility, timeliness, and legal compliance of OSINT make it an invaluable asset for resource-constrained organizations.
While OSINT presents certain challenges, such as data overload, false positives, and data manipulation, adhering to best practices, utilizing specialized tools, verifying information, collaborating with experts, and staying up-to-date can help mitigate these obstacles.
As the cyber crime landscape continues to evolve, OSINT will undoubtedly play an increasingly critical role in ensuring the safety and security of individuals, businesses, and governments. By embracing the power of OSINT, law enforcement, cybersecurity professionals, and security researchers can effectively combat this growing menace and bring cyber criminals to justice.
4 out of 5
| Language | : | English |
| File size | : | 30021 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 434 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Deborah Everett
Deborah Everett Meredith Russo
Meredith Russo Dee Saunders
Dee Saunders David Burch
David Burch Marcia Maxwell
Marcia Maxwell David Harris
David Harris Janet Edwards
Janet Edwards Sonali Dev
Sonali Dev David Nicolle
David Nicolle David Arthur Walters
David Arthur Walters Margreit Maitland
Margreit Maitland Debbie S Culver
Debbie S Culver David Lyon
David Lyon David Brown
David Brown Donald Culross Peattie
Donald Culross Peattie David Lawday
David Lawday David Nicol
David Nicol David R Ross
David R Ross David Mark Brown
David Mark Brown Michelle Knudsen
Michelle Knudsen
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 David PetersonLee and the Boogie Police: The Lee Storybook - An Unforgettable Journey of...
David PetersonLee and the Boogie Police: The Lee Storybook - An Unforgettable Journey of... Bob CooperFollow ·14.2k
Bob CooperFollow ·14.2k Ike BellFollow ·6.1k
Ike BellFollow ·6.1k Grayson BellFollow ·6.8k
Grayson BellFollow ·6.8k Melvin BlairFollow ·7.1k
Melvin BlairFollow ·7.1k Curtis StewartFollow ·13.6k
Curtis StewartFollow ·13.6k Terry BellFollow ·5.5k
Terry BellFollow ·5.5k Kelly BlairFollow ·10.7k
Kelly BlairFollow ·10.7k Felix HayesFollow ·11.5k
Felix HayesFollow ·11.5k
 Aron Cox
Aron CoxMastering Project Management: The Ultimate Guide to...
In today's competitive...
 Dominic Simmons
Dominic SimmonsLet's Build Sue Fliess: Unleash the Polychrome Master...
Chapter 1: The...
 Mason Powell
Mason PowellMaster the Digital Marketing Landscape: Fundamentals of...
In the age of digital...

 Aubrey Blair
Aubrey BlairUncover the Secrets of Ancient Blades and Enchanting...
Embark on an Enchanting Journey into the...
 Shannon Simmons
Shannon SimmonsUnleash the Spooktacular with Spooky Crochet Tutorials...
Prepare to be spooked...
 Cade Simmons
Cade SimmonsImmerse Your Little Ones in a World of Enchantment with...
Nursery rhymes have forever ignited the...
4 out of 5
| Language | : | English |
| File size | : | 30021 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Word Wise | : | Enabled |
| Print length | : | 434 pages |